I’ve written before about how I use Cloudflare Access to provide zero trust access and MFA to my homelab without the need for running local VPN infrastructure, and while that has worked great, there was one app I could never get to work reliably behind Cloudflare: Nextcloud.
The issue with Nextcloud came down to issues with the mobile app, webdav, and CSRF errors that occur when proxied behind Cloudflare. While the web interface worked fine after adjusting some configuration values in Nextcloud, the mobile app never worked because it was unable to handle the MFA captive portal required by Cloudflare Access.
That is, until I discovered the WARP Gateway bypass policy in Cloudflare Access.
What is WARP?
WARP is Cloudflare’s free VPN service running on top of the 1.1.1.1 network. While WARP is free for consumers, WARP also includes an enterprise version called “gateway” that allows Cloudflare Access customers to provide users with a VPN into their Cloudflare network.
WARP with gateway is unlike a traditional corporate VPN because it requires no local hardware or software. Instead, it relies on the existing Cloudflare firewall that is protecting your network through DNS. Because it is implemented through DNS and runs completely in the cloud, it allows you to easily protect network assets in multiple locations, including those that you don’t even host, like SaaS products.
Why not use a traditional VPN?
While a traditional VPN would work fine in my use case where I only need to access one service that is hosted locally, as I wrote in the last zero trust article, I was fed up with running my own VPN and wanted something that was seamless to use, including on “guest” devices, where I don’t need to install extra software or remember a private key.
WARP alone doesn’t satisfy all of these requirements, but in addition to Cloudflare Access with Azure MFA, and the extremely easy process of enrolling a device in WARP gateway, I still retain all the benefits of the zero trust network, with the ability to log in from any browser without additional software, along with the ability to use WARP to bypass MFA.
And while I don’t need to bypass MFA on any of my other apps, the convenience of having a single VPN that logs me into any network, including my services running in Cloudflare Pages / Workers, or SaaS apps, is well worth it.
Setting up Cloudflare Access & WARP
First things first, you need to enroll a device in WARP + gateway in order to use it. Head to 1.1.1.1 to download the WARP client for your device.
Once WARP is installed, follow the instructions here to enroll your device in your organization’s gateway.
Next, we need to configure our Zero Trust organization to support detecting and authenticating with the WARP gateway. In your account settings, open the “Network” section and enable Proxying:

Next, head to the “WARP Client” section of your account settings, and add a new “WARP Client Check” under the “Device Posture” section. From the following page, choose “Gateway” as the attribute to add:
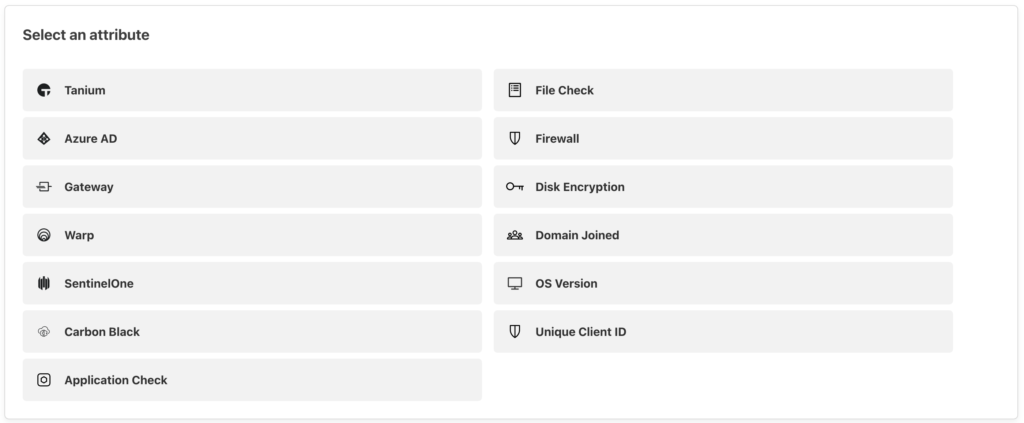
Note that while there is an option for “WARP”, this allows any WARP user, including those with the consumer version, and those not enrolled in your organization to authenticate. “Gateway” on the other hand will only be evaluated to true if a WARP user who is a member of your team and has a device enrolled in your organization is connected.
Finally, after you have enabled WARP detection and authentication, we can add gateway authentication to our app. Head to your desired application and create a new policy.
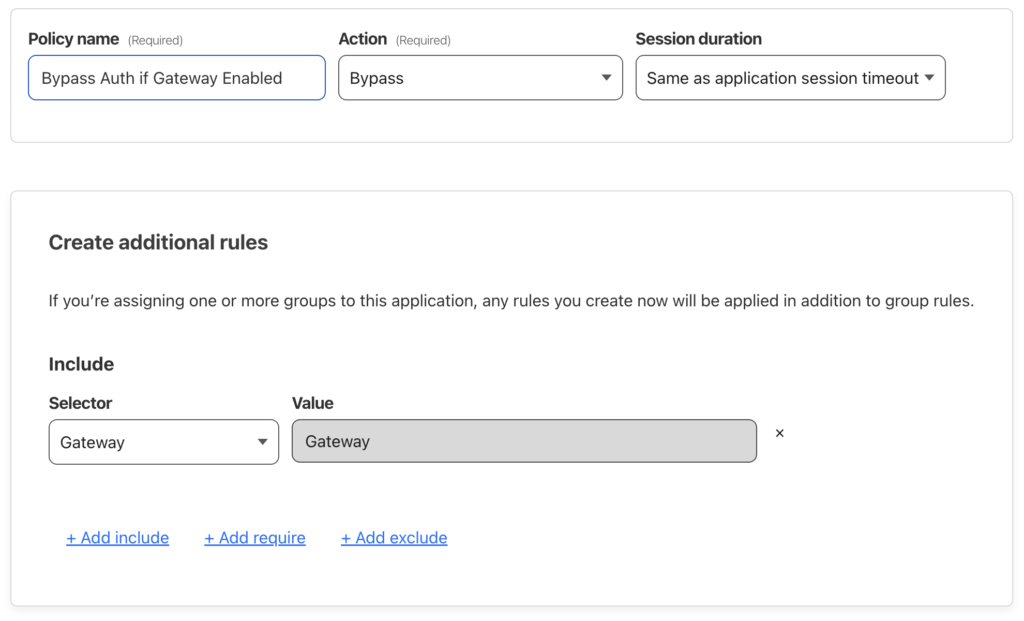
Set the policy action to “Bypass” and create a new “Include” rule with the selector set to “Gateway”. You may want to create this policy in an “Access Group” so you can reuse it.
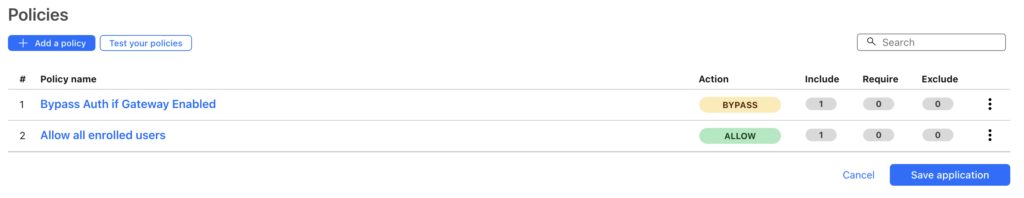
Next you will need to set your “bypass” policy to have a higher priority than your “allow” policies so that users will not see an authentication portal if they have already met the gateway rule.
That’s it! Your enrolled devices should now be able to bypass your Cloudflare Access authentication when WARP is enabled.
To test your policy and ensure that WARP is working correctly, you can visit https://cloudflare.com/cdn-cgi/trace or https://<YOUR-WEBSITE>/cdn-cgi/trace to verify that both WARP and Gateway are on.